Telecom Security Innovation: Mehraj Ali Usman's SIM Swap Detection System Success
Mehraj Ali Usman spearheaded a groundbreaking fraud prevention initiative through the leading Telecom firm's SIM Swap Detection System, which he delivered while navigating complex interdepartmental coordination challenges across one of the nation's largest telecommunications networks. The urgency of this project was underscored by rising industry concerns about SIM swap attacks, which had become increasingly sophisticated and were causing millions in financial losses for customers. His series of innovative security approaches brought outstanding operational success and significantly enhanced customer protection across the telecom giant's infrastructure serving tens of millions of subscribers.
This was a company-wide security system deployment with zero tolerance for detection gaps or performance bottlenecks, as even momentary system failures could expose customers to significant financial risk. The comprehensive fraud prevention framework was developed under Mehraj Ali Usman's guidance, who meticulously orchestrated its architecture across multiple data centers and legacy systems to ensure seamless integration with existing customer service workflows while maintaining real-time detection capabilities across millions of daily transactions. His approach required careful consideration of both technical and human factors, recognizing that the system would need to empower customer service representatives to make quick, informed decisions when potential fraud was detected.
Mehraj Ali Usman's mastery over cross-functional coordination and technical integration was the cornerstone of this success story. A critical liaison between multiple departments, he managed intricate communications among cybersecurity specialists, backend fraud detection engineers, customer experience designers, and fraud operations teams. His creative solution to implement multi-layered detection triggers balanced customer experience concerns with robust security protocols, minimizing legitimate customer friction while maximizing fraud interception rates.
Technical implementation required careful consideration of that firm's vast telecommunications infrastructure. Mehraj Ali Usman conceptualized a sophisticated strategy for integrating advanced machine learning models that could analyze behavioral patterns and flag suspicious SIM activities in real time. This thoughtful architectural approach was key toward effective fraud detection, as well as maintaining seamless service for millions of legitimate customers.
A significant innovation in Mehraj Ali Usman's approach was the establishment of a dynamic threshold adjustment framework that continuously refined the system's accuracy based on evolving fraud patterns and operational feedback. He pioneered a "feedback loop" methodology where fraud analysts could quickly tag false positives and missed detections, allowing the machine learning models to constantly improve without requiring lengthy development cycles. For instance, this adaptive system helped navigate the delicate balance between overly aggressive fraud flagging and potentially missed fraud signals while interacting with multiple operational teams and technology stakeholders simultaneously. The approach was particularly notable for its ability to adjust to regional variations in fraud patterns, automatically tuning detection sensitivity based on geographic risk profiles.
This project created ripples beyond immediate security enhancements. Not only did Mehraj Ali Usman and his team ensure robust implementation and effective operation of the SIM Swap Detection System, but they also elevated the company's reputation in the telecommunications security sector. This translated into considerable business value when the system reduced SIM swap-related fraud by over 30% within just six months of deployment, protecting millions of customer accounts from potentially devastating identity theft and financial losses.
The measured outcomes of this project were substantial and far-reaching. It successfully integrated with existing systems while maintaining stringent performance requirements, with the platform processing over 50,000 SIM change requests daily with sub-second response times. The system additionally exceeded initial protection targets, achieving a 30% reduction in SIM swap fraud within six months compared to the 20% target originally set by executive leadership. It quickly became a benchmark for telecom fraud prevention systems industry-wide, with several technology publications citing the implementation as a case study in effective security architecture.
The project earned significant internal recognition, including an impressive acknowledgment during the company's annual security summit, where executives highlighted Mehraj's exceptional ability to bridge technical security requirements with practical operational realities. The Chief Information Security Officer specifically praised the implementation for achieving the rare combination of enhanced security, improved operational efficiency, and minimal customer friction - objectives that traditionally involve difficult tradeoffs.
Looking forward, this project's success points toward the entire telecommunications security industry and, particularly, to fraud prevention architectures. Mehraj Ali Usman's model of efficient security implementation within complex organizational structures gives future undertakings a precise template. His innovative approaches to stakeholder alignment and technical integration continue to influence practices in the industry, taking place within the evolving landscape of telecom security.
In fact, the architecture of the project set a new standard for fraud detection implementation within the telecommunications industry. Coordinating multiple detection layers and handling varied analytical models demonstrated that comprehensive security solutions could be deployed without compromising customer experience, even at massive scale. The system's ability to maintain a false positive rate below 0.01% while catching sophisticated fraud attempts became a reference point for similar security initiatives. Such successes remain to this day an example for similar programs within the telecommunications ecosystem and contribute to ongoing progress in fraud prevention methodologies, particularly as criminal tactics continue to evolve in sophistication.
The work was successful not only in the immediate term but also served as a foundation for further security enhancements as additional fraud detection modules were subsequently integrated into the framework. The platform's modular design allowed for the later addition of biometric verification layers and device fingerprinting capabilities without disrupting the core detection engine. Mehraj Ali Usman continuously refined his innovative approach toward security architecture and demonstrated remarkable capability in navigating technically complex implementations within operational constraints. The success of the project ensured not only heightened customer protection but also established higher standards of excellence for telecommunications security implementations industry-wide.
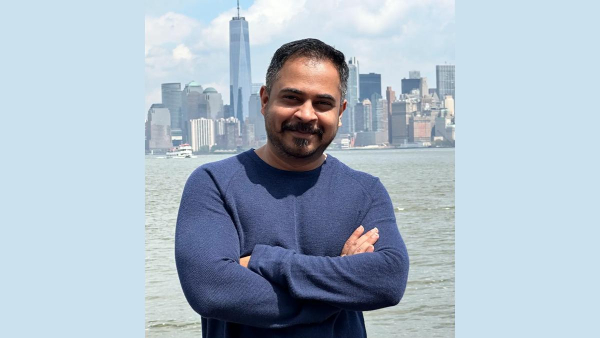
About Mehraj Ali Usman
Known for his technical vision and analytical expertise, Mehraj Ali Usman has distinguished himself through his innovative approach to cybersecurity, fraud prevention, and digital product development. His expertise in implementing sophisticated detection systems and advanced security frameworks has resulted in significant improvements in fraud prevention, including substantial reductions in account takeover incidents through machine learning implementation. With a Ph.D. in Cloud Computing and Big Data Analysis and extensive experience in fintech and telecommunications, Mehraj combines academic excellence with practical expertise to drive technological advancement in security architecture. His comprehensive understanding of regulatory requirements, risk management, and customer experience optimization has established him as a trusted advisor in the telecommunications and financial security sectors, consistently delivering solutions that exceed protection objectives while maintaining exceptional user experiences.













 Click it and Unblock the Notifications
Click it and Unblock the Notifications